7 tips for your business’s cyber security
Cyberattacks can be categorized into active and passive according to their intention. The purpose of active attacks is specifically to attack you. In the case of passive attacks, individuals with malicious intent cast out a wide net and count on the likelihood that someone will get stuck there.
Cyber Risk Insurance - is it worth it?
The Information System Authority of the Republic of Estonia consistently points out that cyber-attacks happen every day. We hear more and more about cases where cybercriminals have been successful.
Deficiencies in cyber hygiene will prove to be expensive
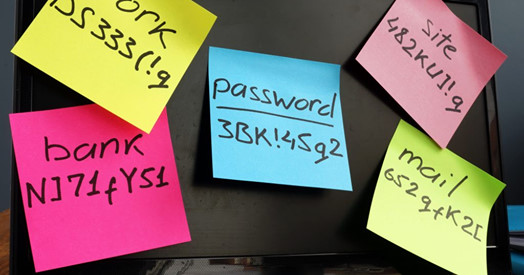
Secure authentication in a digital society is all-important. To ensure security, organisations should enact measures that allow users to use the systems in the safest possible way. It’s long past the time when relying only on a username and password for authentication was adequate. Cyber-attacks are not the “hacking” we know from the movies. It is much easier for the attackers to gain access to a system by using weak, stolen or otherwise compromised authorisation measures. Identity has become a new field of security in combating cyber-attacks.
_block.png)